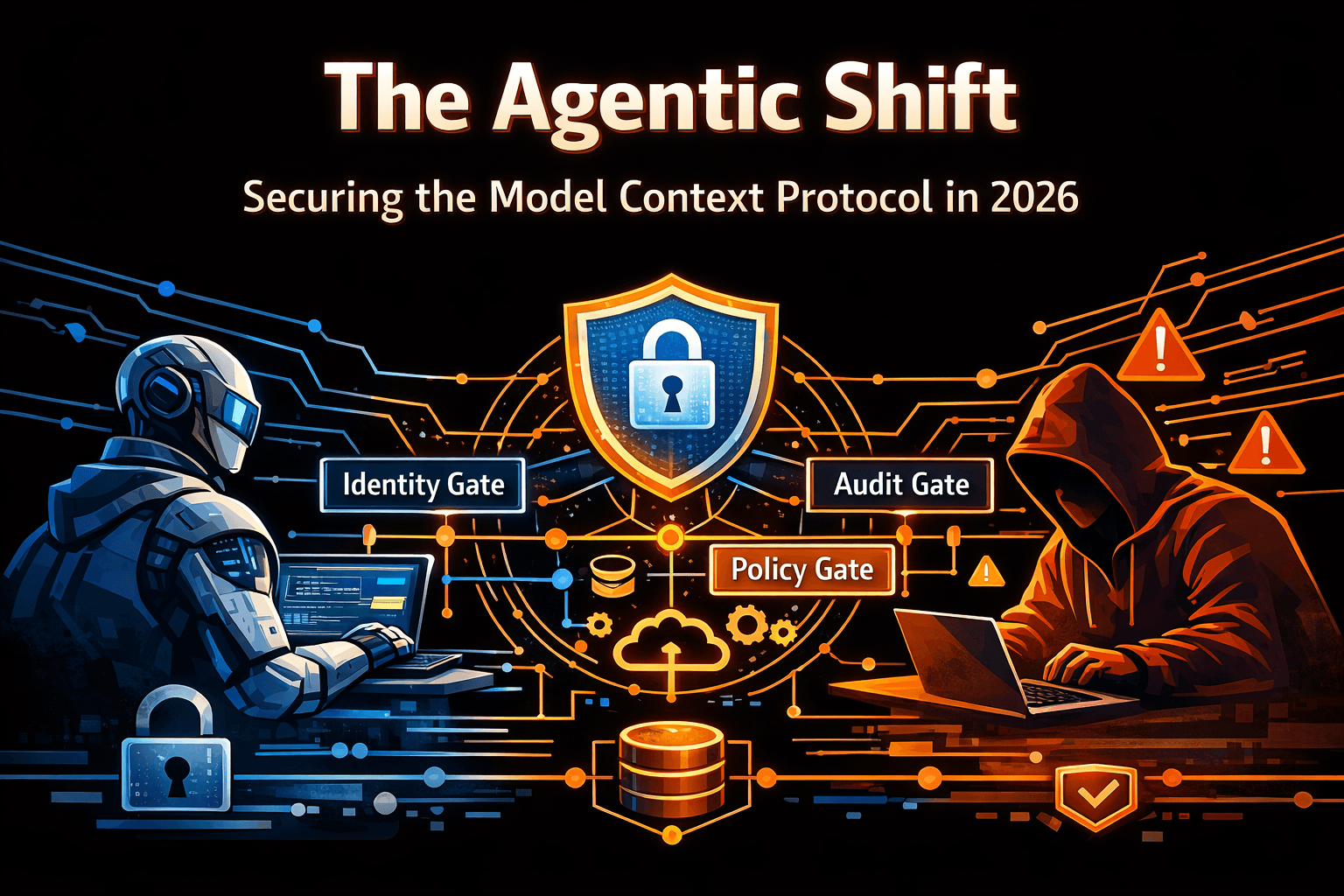
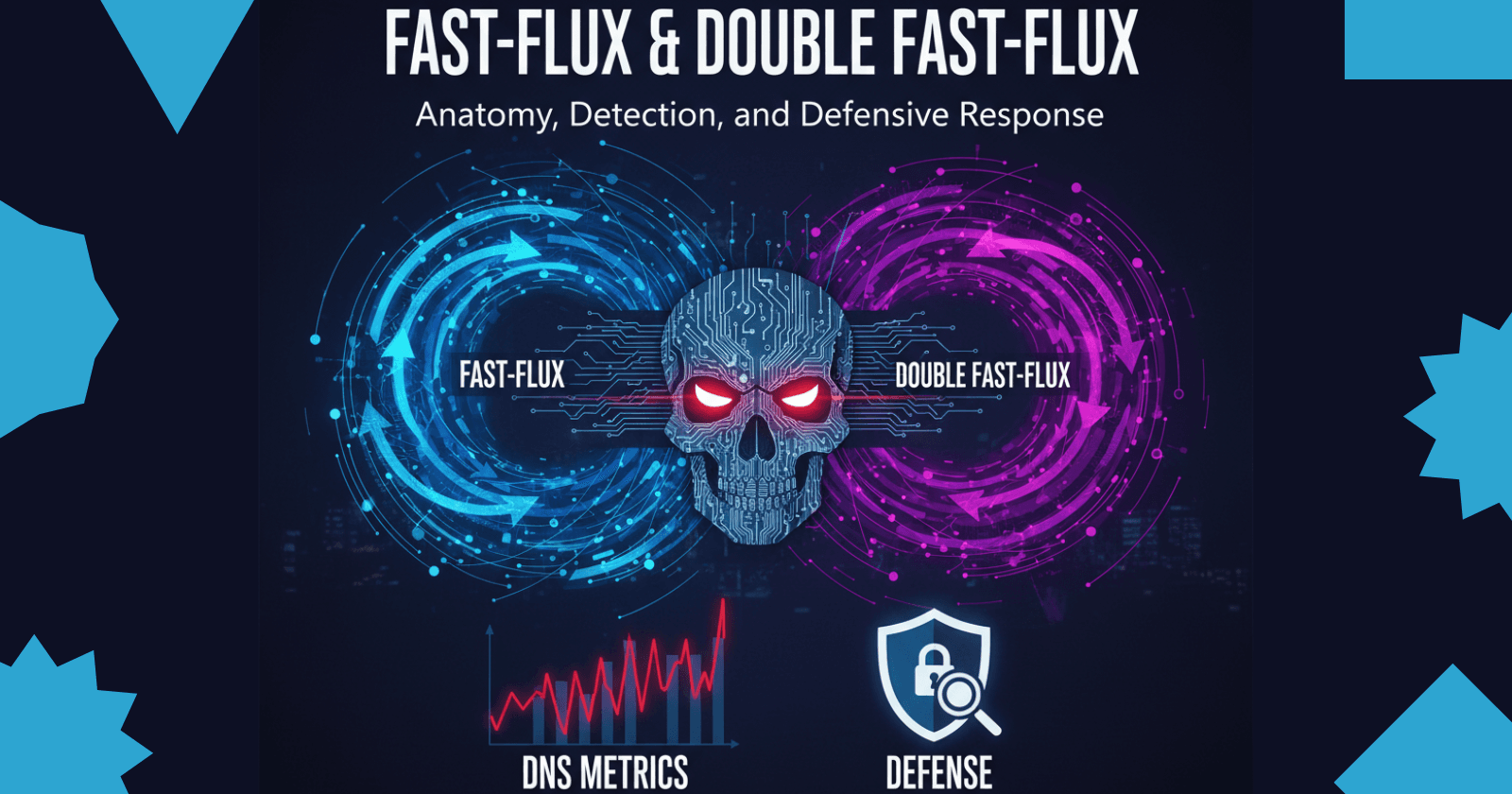
Fast-Flux & Double Fast-Flux: Anatomy, Detection, and Defensive Response
Dive deep into fast‑flux and double fast‑flux DNS techniques. Learn how botnets evade detection, how to detect them using DNS metrics, and how to defe
Executive Summary:
Fast-Flux isn’t sorcery, it’s smart DNS abuse. Attackers rotate a domain through dozens or hundreds of IP addresses (often infected hosts) to obscure the true command-and-control or phishing backend. Think of it as a constantly shifting “hall of mirrors” where every reflection hides the real attacker.
Double Fast-Flux takes it up a notch. Not only do the A/AAAA records change rapidly, but the name servers (NS) themselves are rotated creating a two-layer dynamic infrastructure that’s notoriously hard to take down. Both the front-end proxies and back-end cores keep morphing, frustrating investigators and takedown teams.
DNS fundamentals are key to defense. To detect or dismantle flux networks, defenders must understand A/AAAA records, NS records, TTL behavior, recursive vs. authoritative lookups, DNSSEC, and Response Policy Zones (RPZ). These basics form the blueprint for both the attacker’s design and the defender’s countermeasures.
Detection is all about patterns, not guesses. High IP churn, low TTLs, wide ASN/geolocation spread, and inconsistent reverse DNS often mark flux domains. Effective defense blends passive DNS, resolver logs, TLS certificate telemetry, and endpoint forensics distinguishing flux botnets from legitimate CDNs through behavioral context.
Defense is a team sport. Containment begins with RPZ blocking or sinkholing, followed by forensic preservation, registrar/ISP escalation, and bot cleanup. Sustained defense means coordinating with ISACs, CERTs, and trusted partners sharing indicators responsibly to protect others without alerting the adversary.
Before We Dive In: Let’s Understand the Fundamentals of DNS
Before we jump into the mechanics of fast-flux and double fast-flux architectures, it’s important to step back and unpack the foundation they exploit, the Domain Name System (DNS).
If you’ve ever wondered why DNS matters so much to attackers and defenders alike, this section will make things click.
Think of DNS as the Internet’s distributed phonebook except this phonebook doesn’t live in one place. It’s global, hierarchical, and constantly updated. When you visit a site, your machine isn’t connecting to a name like example.com it’s using DNS to look up where that name currently “lives”, its IP address.
Attackers realized long ago that if they can control how those names resolve or how often they change they can make their infrastructure nearly impossible to pin down.
So, before we talk about flux networks that twist DNS into a self-healing Hydra, let’s first understand how DNS normally works, what record types exist, and why small details like TTLs or NS delegations can make or break your detection.

DNS: The Who’s Who
Let’s start with the main actors in every DNS conversation.
Client / Stub Resolver
The local component on your device (browser, OS, or application) that issues the DNS query.Recursive Resolver (Caching Resolver)
The “middleman” DNS server your device actually talks to. It hunts down answers from other servers if it doesn’t already have them cached. ISPs, enterprises, and providers like Cloudflare or Google often run these.Authoritative Name Server
The source of truth for a specific domain or zone. It holds the definitive DNS records forexample.comand responds to queries with real answers (A, AAAA, NS, MX, TXT, etc.).Root and TLD Servers
The top of the hierarchy. Root servers know where.comor.orglive; TLD servers know which authoritative nameservers manageexample.com.Registrar / Registry
The organizations that register and delegate domain ownership. They control where the NS records at the TLD point, and they’re often involved in takedown or abuse handling.
Pro tip: Always remember that the authoritative name servers are the final source of truth. Everything else is cached, copied, or delegated.
The Core DNS Record Types (and Why They Matter):
DNS has many record types, but for understanding fast-flux, a few are essential.
A and AAAA Records -
A record maps a hostname to an IPv4 address.
Example:www.example.com → 93.184.216.34AAAA record does the same for IPv6.
Example:www.example.com → 2606:2800:220:1:248:1893:25c8:1946
These are the “phone numbers” of DNS. In fast-flux networks, these records are rotated rapidly dozens or even hundreds of IPs, each staying valid for seconds or minutes.
www IN A 93.184.216.34
www IN AAAA 2606:2800:220:1:248:1893:25c8:1946
NS Records -
NS (Name Server) records tell the world which servers are authoritative for a domain meaning, they define where to go to get the real DNS data (A, MX, TXT, etc.) for that domain. In short NS records = the “map” that points resolvers to the right DNS servers for a zone.
example.com. IN NS ns1.example.net.
example.com. IN NS ns2.example.net.
These lines mean that ns1.example.net and ns2.example.net are the official DNS servers for example.com. In double fast-flux, these NS records themselves are constantly changing creating multiple layers of redirection.
CNAME (Canonical Name) -
An alias like a nickname for another hostname.
Example:mail.example.com → mailhost.provider.net
CNAME chains are sometimes abused to hide behind legitimate infrastructure or confuse investigators.
MX (Mail Exchange) Records -
MX records tell mail servers where to deliver emails for a specific domain.
They point to the mail server hostnames responsible for handling incoming email traffic. In short MX record = directs email for a domain to the correct mail server.
Example:
example.com. IN MX 10 mail1.example.com.
example.com. IN MX 20 mail2.backup-example.com.
The number (priority) indicates which server to try first lower values = higher priority. In this example, mail is delivered to mail1.example.com first, and if that fails, it falls back to mail2.backup-example.com.
TXT (Text) Records -
TXT records store arbitrary human- or machine-readable text linked to a domain.
They’re versatile and used for many verification and authentication purposes. In short TXT record = general-purpose field for storing domain-related information.
Example:
example.com. IN TXT "v=spf1 include:_spf.google.com ~all"
example.com. IN TXT "google-site-verification=abc123"
PTR (Reverse DNS) -
PTR (Pointer) records are the reverse lookup of DNS they map an IP address back to a hostname, essentially the opposite of an A record. In short PTR record = reverse DNS entry → IP → hostname.
Example:
34.216.184.93.in-addr.arpa. IN PTR www.example.com.
This means that if someone performs a reverse DNS lookup on the IP 93.184.216.34, it should resolve to www.example.com.
SOA (Start of Authority) -
Contains administrative details for a zone: serial numbers, refresh and expire times, and contact info.
example.com. IN SOA ns1.example.net. hostmaster.example.com. (
2025100401 ; serial
3600 ; refresh
600 ; retry
604800 ; expire
86400 ; minimum TTL
)
Tracking SOA serials can help identify when a zone changes a great signal for monitoring malicious flux domains.
Glue Records -
Glue records are special A or AAAA records provided by the parent zone (usually the TLD) to help resolvers reach a domain’s nameservers when those nameservers are inside the same domain they serve. In simple terms Glue records = the “directions” that tell DNS resolvers how to reach your nameserver when it’s inside your own domain.
Example:
example.com. IN NS ns1.example.com.
example.com. IN NS ns2.example.com.
ns1.example.com. IN A 192.0.2.10
ns2.example.com. IN A 192.0.2.11
Without those A records (the glue), resolvers would fall into an infinite loop, they’d need to query example.com to find ns1.example.com, but ns1.example.com itself is part of example.com.
So, the parent zone (like .com) stores the IPs of these nameservers directly the glue breaking that loop.
Caching, TTLs, and Propagation - the Hidden Timers
Every DNS record comes with a TTL (Time To Live) how long it can be cached.
Short TTLs (e.g., 60s) = data changes fast.
Long TTLs (e.g., 86,400s) = data persists longer.
Attackers love short TTLs, because it forces resolvers to fetch new data constantly meaning new IPs appear all the time.
Legitimate CDNs sometimes also use short TTLs for load balancing, but the patterns differ (we’ll discuss that in detection).
The DNS Resolution Journey - Step by Step
Let’s trace a single lookup, like www.example.com:
Your client (stub resolver) asks the local recursive resolver.
If cached, resolver replies immediately.
If not cached, resolver asks the root servers where
.comlives.Root points it to
.comTLD servers.TLD servers respond with NS records for
example.com.Resolver queries those authoritative servers for an A record.
Authoritative server replies with the IP address and TTL.
Resolver caches the response and sends it back to you.
Pro tip: Every stage of that journey generates telemetry and every one can be monitored for anomalies. Recursive resolver logs alone can tell fascinating stories.
Background & Definitions:
What Is Fast‑Flux?
Fast‑flux is a tactic used by attackers to make the infrastructure behind a malicious domain difficult to track or take down. It works by rapidly changing the DNS records that map a domain name to IP addresses. Unlike a legitimate load balancer where IPs might change occasionally, a fast‑flux domain can point to dozens or even hundreds of IP addresses in a short period. Each IP typically belongs to a compromised machine or a botnet node acting as a proxy. When users resolve the domain, they get a different IP address almost every time.
An analogy: imagine a street con artist who moves to a new corner every few minutes. If the police are following the last reported location, they are always a block behind. Fast‑flux uses DNS’s caching mechanisms to accomplish the same, by lowering the time-to-live (TTL) values and registering new IPs quickly, the authoritative records only live long enough for a single or a handful of clients. According to security research, single fast‑flux networks register and deregister multiple IP addresses with short TTLs for a single domain, making the domain appear to float across the internet.
What Is Double Fast‑Flux?
Double fast-flux takes the idea one step further by also rotating the domain’s Name Server (NS) records.
In single fast-flux, a domain (for example, malicious[.]site) uses multiple A or AAAA records that change rapidly each pointing to a different compromised host acting as a reverse proxy or relay. These front-end hosts handle inbound connections and forward them to a stable backend (the real command-and-control or phishing server). The NS records, which identify the authoritative nameservers for the domain, usually remain constant.
In double fast-flux, attackers add another layer of indirection. They configure the domain’s NS records to point not to stable infrastructure, but to other compromised machines known as flux agents. These flux agents act as temporary, rotating authoritative servers that respond to DNS queries or forward them deeper into the network. The NS records themselves are frequently updated to reference new flux agents, and those agents may also rotate their A/AAAA addresses in the same way as the front-end proxies.
This setup creates a two-tier chain of rotating proxies:
Queries first go to a transient flux agent acting as the domain’s authoritative nameserver.
The flux agent then relays or proxies the request to the hidden backend or next layer of infrastructure.
Both layers the front-end proxy hosts (visible A/AAAA records) and the flux agents (rotating NS layer) typically consist of compromised machines within the botnet.
Brief History and Malicious Use‑Cases
Fast‑flux emerged in the mid‑2000s when botnets like Storm leveraged it to hide phishing pages and command‑and‑control (C2) infrastructure. The technique gained notoriety when the Avalanche botnet used double fast‑flux to run a “bulletproof” hosting operation for spam, Zeus banking trojans, and ransomware. Another example is Conficker, which combined fast‑flux with domain generation algorithms to evade sinkholes and takedowns. Today, fast‑flux continues to appear in phishing campaigns, malware distribution, cryptocurrency scams, and credential‑harvesting sites. Its purpose is always the same: make it harder for defenders to identify the actual server hosting malicious content.
Architecture & How These Techniques Work:
Typical Fast‑Flux Architecture -

The diagram above illustrates how a single fast-flux network operates.
Client Request:
The victim’s system initiates a DNS query for a malicious domain (e.g.,badexample[.]com).Recursive Resolver & Cache:
The resolver checks its local cache for existing records.If found (cache hit), the stored IPs are returned.
If not (cache miss), the resolver proceeds with external resolution.
RPZ / Sinkhole Check:
Before contacting the DNS hierarchy, the resolver consults the Response Policy Zone (RPZ).If the domain is listed as malicious, the resolver blocks or sinkholes it.
If not, the query continues to the attacker’s authoritative nameserver.
Authoritative Name Server:
The attacker-controlled authoritative NS returns multiple A/AAAA records each pointing to compromised front-end proxy hosts.These records have very short TTLs (seconds or minutes), causing rapid rotation.
Each DNS query may yield a different set of proxy IPs.
Front-End Proxies:
The client connects to one of the returned proxy IPs.These proxies are infected hosts spread across diverse networks and geographies.
They act as disposable relays, forwarding traffic to the backend server.
Backend C2 (Hidden Core):
The stable backend system hosts the real malicious content or command-and-control (C2) service.- Proxies tunnel traffic to this backend, shielding it from direct discovery.
Defensive Implication:
Because IPs rotate so rapidly, defenders can’t rely on static blocklists.
The key indicators are short TTLs, high IP churn, and distributed ASNs across responses.
Summary: Single fast-flux = stable authoritative nameserver + rapidly rotating A/AAAA records (proxies) that obscure a fixed backend C2.
Double Fast‑Flux Architecture -

The diagram above illustrates how double fast-flux extends the single fast-flux model by adding a second layer of rotation at the DNS delegation level.
Client / Stub Resolver:
The victim initiates a DNS query for a malicious domain (e.g.,badexample[.]com).Recursive Resolver (Caching):
The resolver checks its cache and Response Policy Zone (RPZ).If cached, it returns the stored IPs.
If blocked by RPZ, the query is sinkholed or denied.
Otherwise, it continues to resolve the domain.
Flux Agents (Rotating Authoritative NS):
Instead of querying a fixed authoritative nameserver, the resolver contacts a pool of flux agents, compromised machines temporarily acting as authoritative NS servers.These flux agents themselves rotate frequently.
Each may either delegate further or directly return A/AAAA records pointing to front-end proxies.
Front-End Proxies (Compromised Hosts):
The resolver’s response contains multiple short-TTL proxy IPs.These proxies relay user traffic to the backend C2.
IPs change frequently, with old ones dropped and new ones added as bots go offline or rejoin.
Backend C2 (Hidden Core):
The real attacker infrastructure a stable set of servers that receive proxied connections from front-end hosts.- May host phishing sites, C2 logic, or data exfiltration endpoints.
Flow Summary:
Resolver queries rotating flux agents (NS layer).
Flux agents return or delegate to rotating proxy IPs (A/AAAA layer).
Client connects to a proxy, which tunnels traffic to the hidden backend C2.
In essence: Double fast-flux = rotating NS + rotating A/AAAA.
Both the delegation and data layers are in flux, maximizing resilience and takedown resistance.
Lifecycle of a Fluxed DNS Record -
Registration: The attacker registers a domain, often through a compromised registrar account or a fly‑by‑night registrar. They point the domain’s NS records to servers they control.
Flux agent enlistment: The attacker recruits compromised hosts (botnet nodes) as front‑end agents. They update the A/AAAA records for the domain to include the IPs of these agents. For double flux, they also update the NS records to point to flux agents.
Low TTL rotation: The TTL values on A/AAAA and/or NS records are set to a few minutes. When resolvers cache the record, it soon expires and the resolver must query again, picking up new IPs. The attacker’s authoritative server constantly cycles IP addresses in and out of the record set.
Traffic proxying: When a victim visits the domain, their request goes to a front‑end agent. That agent forwards the connection to a back‑end server, often over an encrypted channel. The front‑end may also perform SSL/TLS termination or simply relay packets.
IP churn: Over time, different bots are rotated into the record set. Bots that go offline or are taken down are removed; new bots are added. For double flux, the name servers themselves are also rotated among bots.
This lifecycle makes the malicious infrastructure extremely resilient: if a few agents are taken down, others take their place. If a registrar suspends the domain, attackers can switch to a new domain name and re‑reuse the same botnet.
Differences Between Single and Double Fast‑Flux -
Single fast‑flux involves only the rotation of the A/AAAA records (front‑end proxies) while the NS records remain static. Double fast‑flux rotates both A/AAAA and NS records.
| Feature | Single Fast-Flux | Double Fast-Flux |
| A/AAAA Rotation | ✅ Yes - IPs of front-end proxies change frequently | ✅ Yes - same behavior as single fast-flux |
| NS Rotation | ❌ No - authoritative name server remains static | ✅ Yes - NS records also rotate via flux agents |
| Resilience | Moderate - backend can still be disrupted if authoritative NS is taken down | High - both delegation and proxy layers rotate, making takedowns harder |
| Complexity | Lower - simpler DNS structure with stable delegation | Higher - dual-layer DNS control and synchronization required |
| Detection Signals | Rapid IP churn, short TTLs, and geographically scattered IPs | IP churn + NS churn, frequent delegation updates, multi-layer entropy |
| Common Use Cases | Spam delivery, phishing sites, basic malware distribution | Botnet C2 networks, bulletproof hosting, resilient command channels |
Motivation & Attacker Goals:
Why would an attacker bother with such complexity? The answer lies in the inherent weaknesses of DNS. DNS was designed in an era of trust, with little built‑in authentication or abuse mitigation. Malicious actors exploit this by using fast‑flux to achieve several objectives:
Resilience and Redundancy: By constantly rotating IPs across many compromised machines, attackers ensure that their service remains online even if many nodes are taken down. A single IP or server cannot be easily shut down.
Evasion of Blocklists: Automated blocklists often rely on static IP addresses or hostnames. When a domain points to hundreds of unique IPs across multiple networks and autonomous systems, it is harder to block them all.
Takedown Resistance: When law enforcement or abuse teams attempt to seize or disable a server, the infrastructure can quickly move elsewhere. Double fast‑flux further complicates this by rotating name servers and placing the true backend behind multiple layers of proxies.
Proxying and Traffic Scrubbing: The front‑end bots act as reverse proxies, shielding the backend from direct detection. They can also filter or scrub traffic, for example by only forwarding connections that look like victims rather than researchers.
Cost Efficiency: Using compromised machines as infrastructure is cheaper than renting legitimate hosting. Attackers can conscript thousands of devices and cycle through them, essentially crowdsourcing their hosting.
Real‑world criminal operations like Avalanche used double fast‑flux to host phishing sites, exploit kits, and malware while staying operational for years. Similarly, bulletproof hosting services may incorporate fast‑flux to give clients an infrastructure that is difficult to seize.
Common Indicators & Detection Signals:
Detecting fast‑flux or double fast‑flux networks requires looking at DNS patterns, network telemetry, and endpoint logs. Here are common indicators:
DNS Churn Metrics -
Unique IP count and answer set size: Malicious fast‑flux domains often return many unique IP addresses. Research has shown that fast‑flux domains can have dozens or hundreds of IPs, whereas legitimate domains (except CDNs) typically have a small, static set. A high average answer length (e.g., >10 IPs) is suspicious.
TTL Distribution: Legitimate domains usually use TTL values between several minutes and a day. Fast‑flux domains use very low TTLs (e.g., 0–600 seconds) to force rapid re‑resolution. Filtering queries with TTL > 1800 s can help separate normal traffic from suspicious domains.
NS Churn: For double fast‑flux, the number and variety of NS records is a strong signal. Multiple NS records with low TTLs, high churn, and IPs across many networks or ASNs indicate fast‑flux.
ASN/Geography Entropy -
Autonomous System (AS) Count: Fast‑flux domains often have IPs across many ASNs. The AS‑fraction metric (
(nAS - 1)/nIP) quantifies the dispersion: values closer to 1 indicate each IP is in a different ASN. Legitimate CDNs usually operate within a few ASNs.Geographic Dispersion: Fast‑flux IPs often spread across many countries. If a domain’s IPs span numerous continents with no clear pattern, it may be a sign of a botnet rather than a global CDN.
Reverse DNS Mismatches -
Look up the reverse DNS entries of the IP addresses returned for a domain. If the PTR records point to residential DSL or cable hosts or contain dynamic IP names (e.g., 123-45-67-89.dynamic.isp.net), the domain may be using compromised home PCs as proxies. Conversely, legitimate services typically resolve to meaningful hostnames related to the provider.
Certificate/HTTP Fingerprinting -
Although DNS churn is a primary signal, combining it with HTTP or TLS fingerprinting can boost accuracy. If the same TLS certificate or HTTP server header is observed on many IPs across different networks, it suggests those IPs are proxies for the same backend. For example, a phishing kit may reuse a self‑signed certificate on every front‑end node. Similarly, identical Server headers, cookies, or HTML responses across many IPs indicate a common backend.
Example Detection Heuristics -
Below is a simplified pseudocode for a detection heuristic. This is for illustration only and should be tuned to your environment.
// pseudocode
// detection logic (illustrative only)
function scoreFastFlux(domain, pdnsData):
ips = collectUniqueIPs(domain, pdnsData)
ttlValues = collectTTLs(domain, pdnsData)
asns = collectASNs(ips)
nsRecords = collectNS(domain, pdnsData)
nsIPs = collectUniqueIPs(nsRecords, pdnsData)
score = 0
if count(ips) > 50:
score += 2
else if count(ips) > 10:
score += 1
if median(ttlValues) < 600:
score += 2
if entropy(asns) > 0.7:
score += 2
if count(nsRecords) > 3:
score += 1
if median(ttl(nsRecords)) < 600:
score += 1
if count(nsIPs) > 10:
score += 2
return score
// A threshold (e.g., score >= 5) can flag a domain as likely fast-flux.
Note: Real implementations should include baseline statistics, whitelists, and machine‑learning models. Consider legitimate CDNs and SaaS providers that might also show some of these behaviors but are benign.
Data Sources & Telemetry to Collect (Forensics):
Effective fast‑flux detection and response depends on comprehensive telemetry. The following data sources can be collected within a security operations center (SOC):
Passive DNS (pDNS): pDNS provides historical data about domain resolution patterns, including the set of IPs, TTLs, and timestamps. Use it to compute IP churn, TTL distributions, and AS dispersion.
Resolver Logs: Internal DNS resolver logs show query volume, requester IPs, query times, and responses. Monitor which clients are resolving suspicious domains and how often.
Web Proxy Logs: HTTP/S proxies record outbound requests, including hostnames, URIs, HTTP methods, user agents, and status codes. This helps attribute domain queries to specific users and identify the type of content served.
TLS Certificates: Collect certificate information (issuer, subject, serial number) during SSL/TLS handshakes. Identical certificates across multiple IPs can indicate a common backend.
WHOIS and Registrar Metadata: Domain registration date, registrar, and registrant details can provide context. New domains registered by obscure registrars may be suspicious.
Endpoint Detection and Response (EDR) Artifacts: Host‑level logs show which processes initiated network connections, file creation, registry changes, and memory indicators. EDR data can confirm infection and support remediation.
Packet Captures: Full‑packet captures or network sensor logs can reveal HTTP/S payloads, TLS handshakes, and DNS query/response patterns. Preserve as much context as possible (source and destination IPs, ports, timestamps).
Certainty of Timestamps: Always record accurate timestamps when collecting forensics. In a fast‑flux environment, IP assignments change quickly; aligning logs by time is critical for correlation.
When collecting these data, ensure compliance with privacy laws and organizational policies. Use encryption and access controls to protect sensitive information.
False Positives & How to Tune?
Fast‑flux detection can generate false positives, especially with legitimate Content Delivery Networks (CDNs), Anycast services, or dynamic DNS providers. To tune your analytics:
Baseline legitimate CDNs: Record the behavior of major CDNs (Cloudflare, Akamai, Amazon CloudFront). They also rotate IPs and use low TTLs, but their ASNs and ranges are well‑known. Maintain a whitelist of legitimate CDN IP ranges.
Evaluate domain age and registrar: Many malicious domains are registered days before being used. Conversely, legitimate domains often have long registration histories and established registrars.
Cross‑reference with TLS certificates: CDNs usually use certificates from reputable certificate authorities. Fast‑flux front‑ends often present self‑signed or mismatched certificates.
Use domain reputation and context: A brand‑new domain with high IP churn is suspicious. A known brand’s domain with similar behavior may be a CDN or a global network.
Analyze service content: If the domain serves static assets, images, or legitimate content distribution patterns, it may be a CDN. If it hosts phishing pages, malware, or odd HTML forms, treat it as malicious.
Tune your detection threshold to minimize noise. For example, increase the required IP count or reduce the weight of TTL in scoring. Combine DNS data with HTTP fingerprinting and endpoint telemetry. Consider supervised machine learning: train a classifier on labeled datasets of known fast‑flux and CDN domains to learn differences in feature distributions.
Response & Mitigation Playbook (Defensive):
When you identify a fast‑flux or double fast‑flux domain, follow a structured response:
Immediate Containment Steps -
Block via RPZ: Add the domain and its known subdomains to your resolver’s RPZ. Redirect queries to a sinkhole IP or return NXDOMAIN. This prevents clients from resolving the malicious domain.
Network Blocking: Use firewalls or proxies to block outgoing connections to the domain and the IP addresses identified in pDNS. Consider blocking entire IP ranges or autonomous systems if they are exclusively malicious.
Evidence Preservation: Preserve DNS logs, resolver caches, packet captures, and any relevant host logs. Fast‑flux IP assignments change rapidly, so timely evidence capture is essential.
Alert and Quarantine Affected Hosts: Identify internal hosts that queried the domain. Isolate them from the network if possible and begin endpoint investigation.
Notify Stakeholders: Inform management, incident response teams, and legal counsel. If the domain is part of a larger campaign, coordinate with threat intel groups.
Escalation and External Coordination -
Registrar/Abuse Reporting: File an abuse report with the domain registrar or hosting provider. Provide evidence (timestamps, IP addresses, logs) to support the case. Some registrars require additional forms or law enforcement involvement.
ISP Coordination: If compromised machines in your network are acting as flux agents, work with your ISP or network provider to remediate the infections. Notify them of the IP addresses used.
Law Enforcement: For large campaigns, coordinate with national CERTs or law enforcement agencies. They may have active investigations and can help with takedown operations.
Long‑Term Remediation -
Bot Cleanup: Clean infected hosts on your network. Use EDR tools to detect malware, remove it, and patch vulnerable software.
Patch and Harden Systems: Fast‑flux often leverages vulnerable devices (routers, IoT). Enforce secure configuration, patch management, and network segmentation.
Improve Telemetry: Enhance your DNS and network logging to monitor suspicious patterns. Deploy sensors at network boundaries and enable certificate logging.
Continuous Monitoring: Set up ongoing detection rules and dashboards in your SIEM. Review them regularly and adjust thresholds based on new threats.
Training and Awareness: Educate SOC analysts and IT staff about fast‑flux indicators and response procedures. Share lessons learned across teams.
Example Abuse Report Checklist -
When filing an abuse report to a registrar or hosting provider, include:
Domain name and subdomains
Description of the malicious activity (phishing, malware, etc.)
Evidence of fast‑flux (pDNS logs showing IP churn, low TTLs)
List of IP addresses and associated timestamps
Screenshots or captured content (if appropriate)
Your contact information and organization details
Request for domain suspension or takedown
Be clear, factual, and concise. Avoid sharing sensitive internal information. Provide citations to laws or policies if necessary.
Detection Implementation Examples (Defensive Code/Pseudocode):
Here are additional pseudocode snippets to illustrate defensive implementations. These examples focus on detection and alert generation within a SIEM.
Scoring a Domain Based on Flux Features -
// pseudocode
// detection logic (illustrative only)
function computeFluxFeatures(domain, pdnsRecords):
features = {}
features.uniqueIPCount = countUniqueIPs(domain, pdnsRecords)
features.uniqueNSCount = countUniqueNS(domain, pdnsRecords)
features.ttlMedian = medianTTL(domain, pdnsRecords)
features.asnCount = countUniqueAS(domain, pdnsRecords)
features.ipGeoEntropy = computeGeoEntropy(domain, pdnsRecords)
return features
function classifyDomain(features):
score = 0
if features.uniqueIPCount > 50:
score += 3
else if features.uniqueIPCount > 20:
score += 2
else if features.uniqueIPCount > 5:
score += 1
if features.uniqueNSCount > 3:
score += 2
if features.ttlMedian < 600:
score += 2
if features.asnCount > 10:
score += 2
if features.ipGeoEntropy > 0.5:
score += 1
return score >= 6
Generating Alerts in a SIEM -
// pseudocode
// detection logic (illustrative only)
for each domain in pdnsFeed:
features = computeFluxFeatures(domain, pdnsFeed[domain])
if classifyDomain(features):
alert = {
"domain": domain,
"uniqueIPs": features.uniqueIPCount,
"uniqueNS": features.uniqueNSCount,
"asnCount": features.asnCount,
"ttlMedian": features.ttlMedian,
"geoEntropy": features.ipGeoEntropy,
"timestamp": currentTime()
}
sendToSIEM(alert)
Fingerprinting Content Similarity -
Use hashing to detect identical content served from different IPs. If a domain’s IPs return the same HTML hash, they are likely proxies for a single backend.
// pseudocode
// detection logic (illustrative only)
function fingerprintContent(url):
response = httpGet(url)
if response.statusCode == 200:
return sha256(response.body)
else:
return null
function compareFingerprints(domain, ipList):
hashes = {}
for ip in ipList:
url = "http://" + ip + "/"
hash = fingerprintContent(url)
if hash != null:
hashes.add(hash)
return hashes.size == 1 // true if all hashes identical
These examples are vendor‑neutral and rely on standard data structures and functions. Adapt them to your environment and integrate them with your logging pipeline.
Monitoring, Threat Intel Sharing & Collaboration:
Fast‑flux detection and response benefit from community cooperation. Share indicators, but do so responsibly:
Join ISACs and CERTs: Industry Information Sharing and Analysis Centers (ISACs) and national Computer Emergency Response Teams (CERTs) facilitate confidential sharing of indicators of compromise (IOCs). Participate actively to receive timely updates.
Use Structured Formats: Share data in structured formats (e.g., STIX, TAXII) that include context, confidence scores, and handling instructions.
Preserve Anonymity and Privacy: Remove sensitive internal IP addresses or user identifiers. Avoid revealing your detection capabilities to adversaries.
Coordinate Response: When multiple organizations see the same fast‑flux campaign, coordinate takedown or blocking. Combined reporting to registrars increases the chance of domain suspension.
Feedback Loops: Collaborate with academic researchers, security vendors, and law enforcement to refine detection heuristics. Provide anonymized datasets for research and improvement of machine‑learning models.
Checklist & Quick Playbook
| Step | Description |
| Detection | Monitor DNS logs and pDNS for high IP churn, low TTLs, multiple NS records, and high ASN dispersion. Use scoring heuristics and fingerprinting. |
| Containment | Add domain/IP to RPZ, block at firewalls or proxies, isolate infected hosts, collect and preserve evidence. |
| Remediation | Clean infected hosts, patch vulnerabilities, harden infrastructure, improve logging, and adjust detection thresholds. |
| Reporting | File abuse reports with registrar/hosting provider, involve law enforcement if necessary, and share indicators via ISAC/CERT channels. |
| Post‑Incident | Hold a debrief, refine detection rules, update playbooks, and educate analysts. |
Tweet‑Sized Key Takeaways:
Fast‑flux hides malicious domains by rotating IPs with low TTL values. Double flux rotates name servers too. Learn the difference and detection techniques.
High IP churn, low TTLs, many ASNs, and rotating NS records are red flags. Use passive DNS and resolver logs to spot them.
Legitimate CDNs also rotate IPs. Reduce false positives by whitelisting known providers and combining DNS metrics with HTTP fingerprints.
RPZ blocking, evidence preservation, and coordinated abuse reporting are key containment steps for fast‑flux incidents.
Build a safe lab with your own domain, containers, and resolvers to simulate fast‑flux behavior and tune detection heuristics.
Share indicators via ISACs and CERTs using structured formats like STIX to help others without tipping off adversaries.
Suggested High‑Quality References:
“Fast Flux – Fast Flux Detection Techniques: A Survey” – IJERT. Discusses definitions and detection metrics.
“Fast Flux Service Network Detection via Data Mining on Passive DNS Traffic” . Explores metrics like IP counts, TTL distributions, AS‑fraction.
“DNS‑Based Fast‑Flux Botnet Detection Approach” . Describes detection process and metrics.
Cloudflare DNS Glossary: Resources on A/AAAA, NS records, recursive vs. authoritative servers
Fortinet Cyber Glossary: Fast‑Flux Networks – Provides high‑level explanation of fast‑flux and detection techniques.